Tricky Spam Emails
Phishing emails are a common occurance where malicious senders will attempt to steal your personal information or passwords by pretending to be a trusted sender. Typically, you would receive an email that appeared to come from a trusted sender, such as a bank or any other frequently visited site that could house a lot of personal information. In this email it usually contains a link to a site with requests that you go to a familiar website to check on the status of something. Sometimes these emails threaten account closure, ask you to change your password, or even suggest an important message that requires urgent attention. Recently we have come across a more advanced scam that was very troubling. This email contains three tricks which are designed to increase the likelihood of users falling for this type of email.
Trick 1 - The Redirect
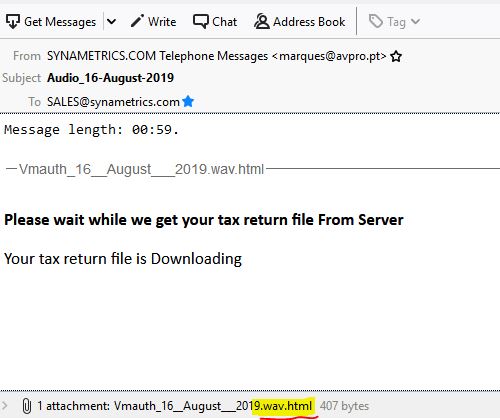
The first trick is that within the email, it has a .wav.html file, and the email is talking about a voicemail. The user would see .wav, which could be similar to other voicemail emails they get, and click on it and it thinking that it will play a message, however, it will actually open up a browser and take them to a specific web page . This web page is where trick two comes in.
Trick 2 - The Fake Login Form
For trick two, the user is taken to a fake page, that is designed to look exactly like the Microsoft Outlook login page. The page also contains the email address of the user already pre-placed in the login field, with the password field blank. The goal of this is to trick the user into thinking they need to log in and they've been to this page before because it already has the email address filled in. This is done by copying the email address from the recipient. If you look at the code of the email, it actually contains a variable for the recipient as username, so they could theoretically send this email to millions of people and all of them would have their own email in the login field. If the recipient is a frequent user of Microsoft Outlook, this might seem similar to them and it could cause them attempt to login.
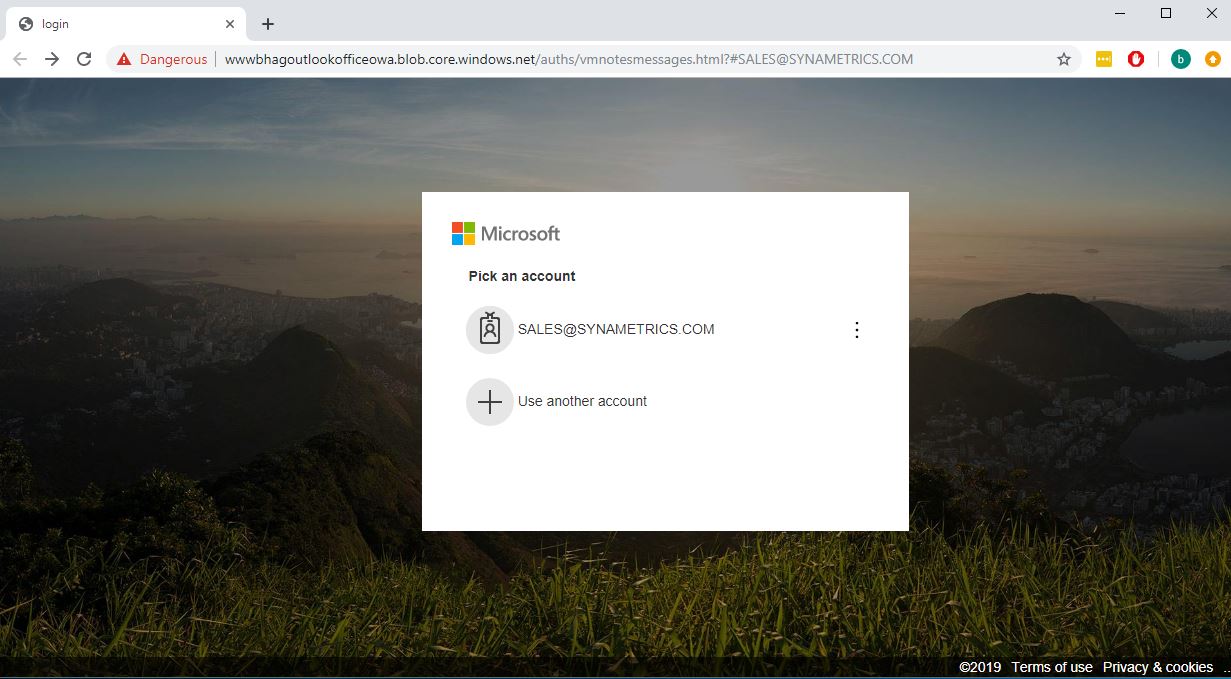
Trick 3 - The Trusted Certificate
Trick three is slightly less noticeable but quite dangerous. This fake site is hosted on Microsoft Azure, so the site appears to have a valid Microsoft certification, when in reality, it should not. This is more of a time frame issue. Eventually, Microsoft will take this page down, as hosting a scam on their platform is not something that interests them. However, this can take a number of days before they are even aware it is happening, and until then, this trick makes it easier for unsuspecting recipients to fall for this scam. Microsoft is usually quick to act and revoke these certificates, as you can see, within the three days this link was active, they had revoked the certificate and marked it as dangerous. However, there was still a multi-day period where users could have been fooled.
All three of these tricks can be used to mislead an unsuspecting user into having their email password stolen. However, with Xeams SMTP server, these emails will be blocked before even reaching your inbox, saving your users, and administrators, a lot of effort.
| Created on: | Sep 6, 2019 |
| Last updated on: | Mar 17, 2026 |
